Malware analysis Malicious activity
Por um escritor misterioso
Last updated 24 outubro 2024

MetaDefender Cloud Advanced threat prevention and detection

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

TryHackMe Hacktivities

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

MetaDefender Cloud Advanced threat prevention and detection

Robust Malware Detection Models: Learning From Adversarial Attacks and Defenses - Forensic Focus
Interactive Online Malware Sandbox

Feature Extraction and Detection of Malwares Using Machine Learning

Malware Analysis Framework v1.0

What is Malware? Definition, Types, Prevention - TechTarget

Mastering Malware Analysis
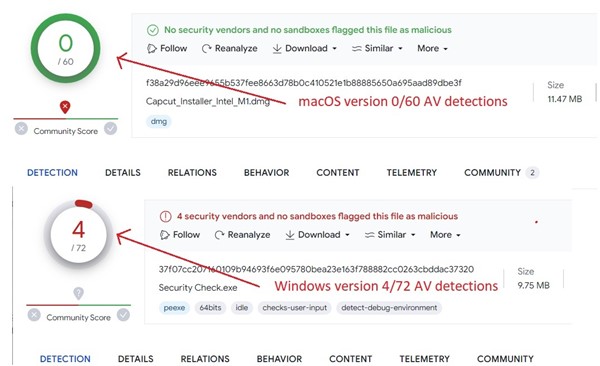
Behind the Scenes: JaskaGO's Coordinated Strike on macOS and Windows
Recomendado para você
-
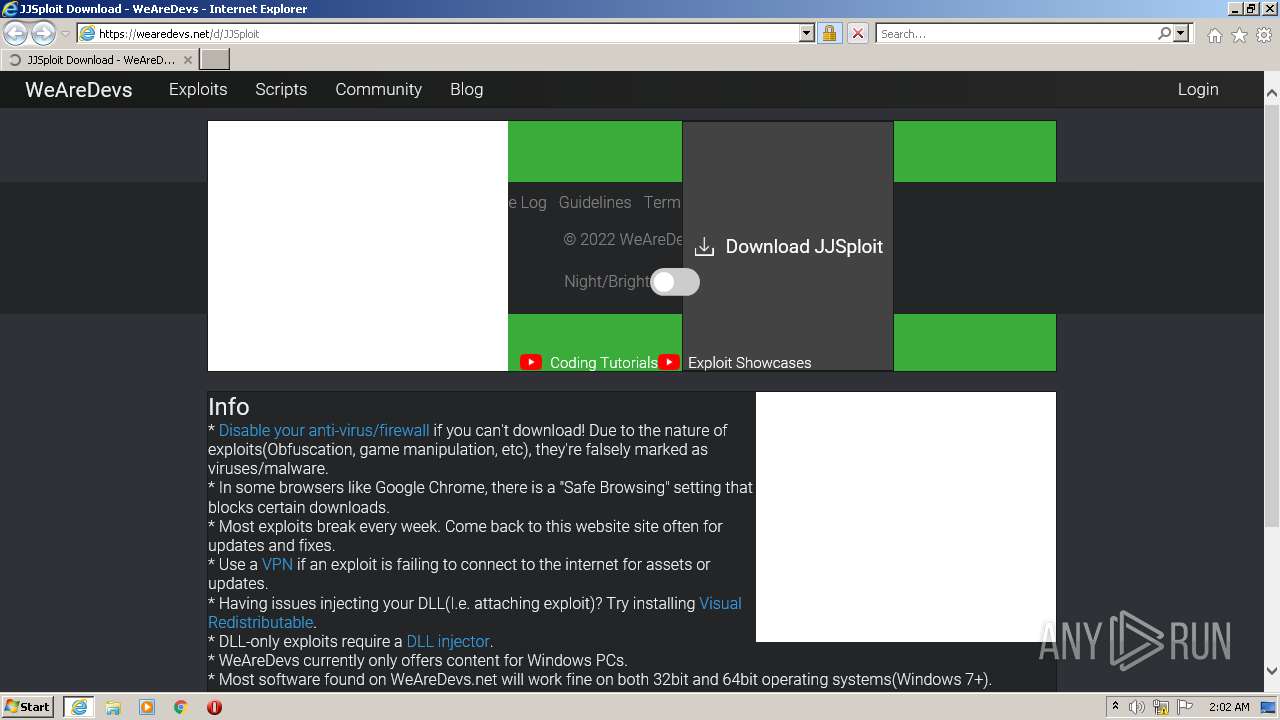
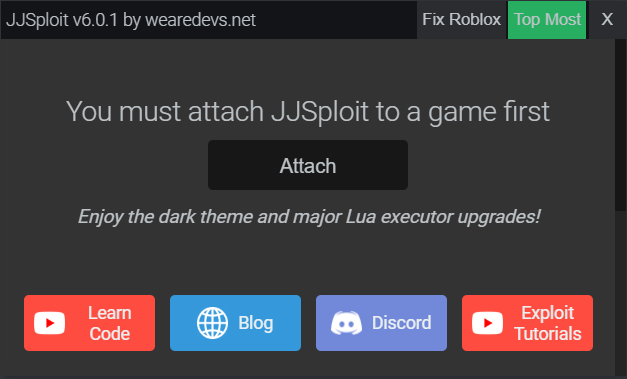 JJSploit Information - WeAreDevs24 outubro 2024
JJSploit Information - WeAreDevs24 outubro 2024 -
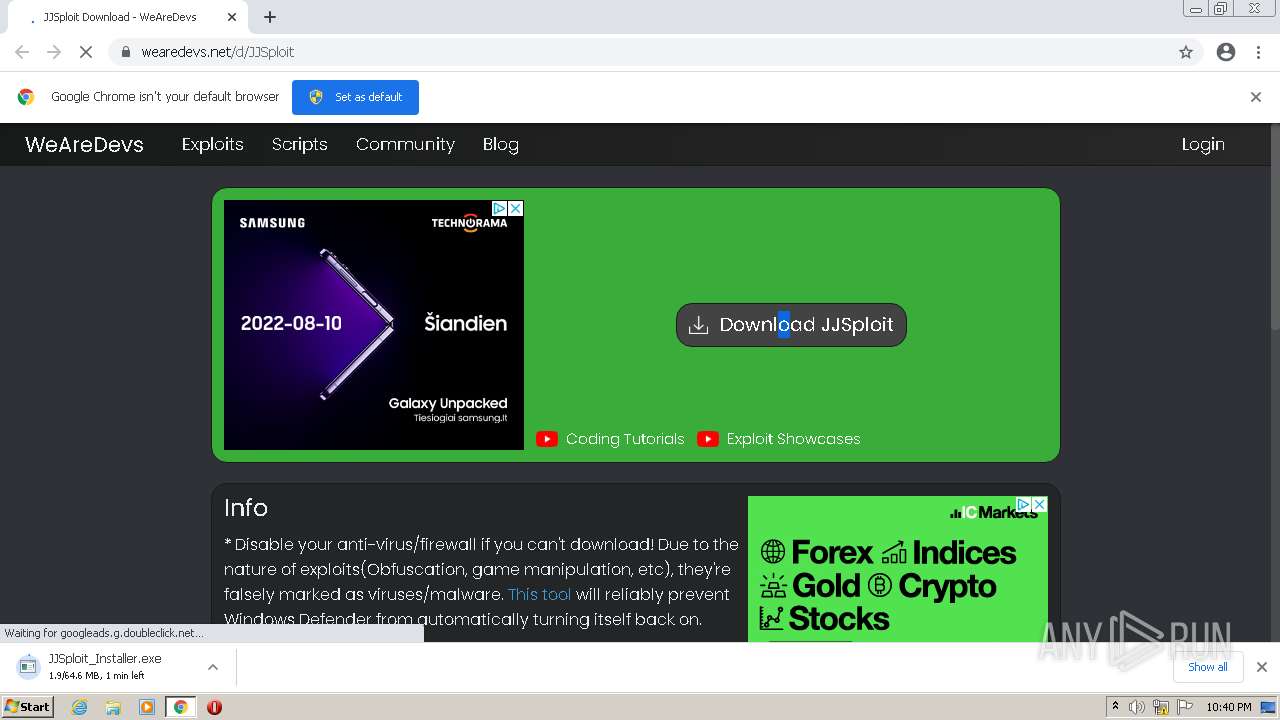
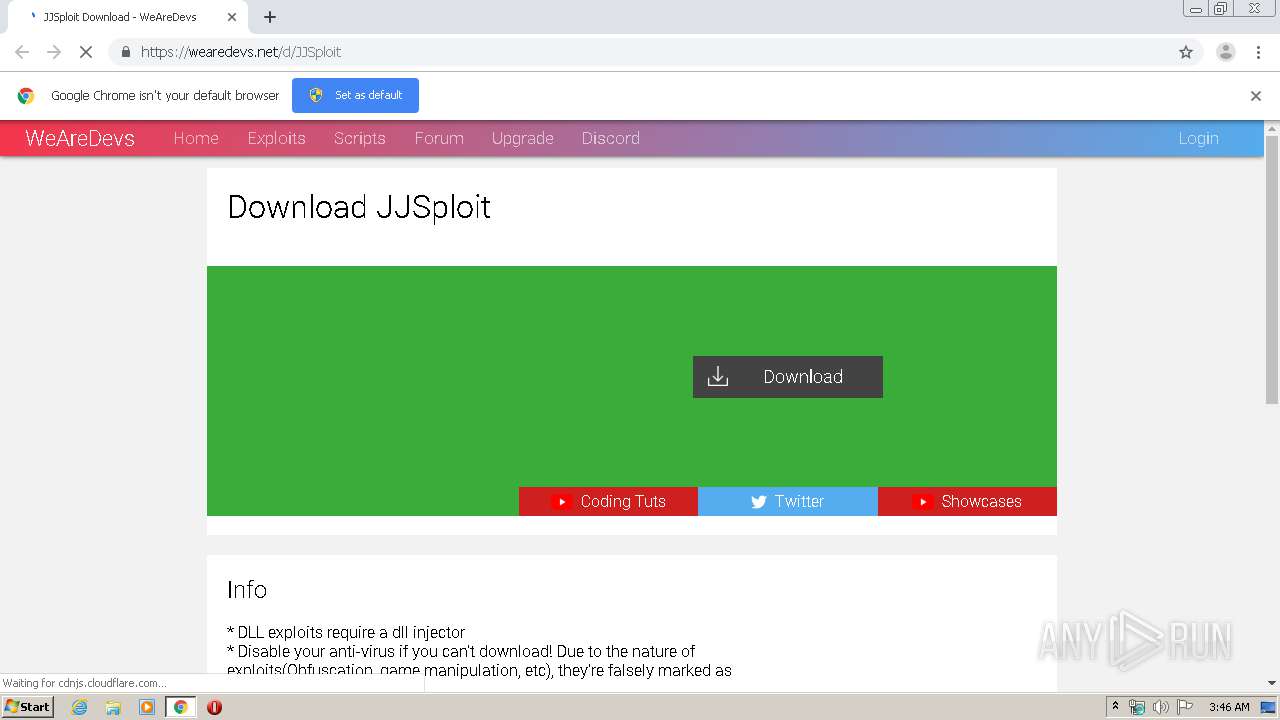
_how-to-download-jjsploit-in-2023-working.jpg) Jjsploit V4 Download Roblox - Colaboratory24 outubro 2024
Jjsploit V4 Download Roblox - Colaboratory24 outubro 2024 -
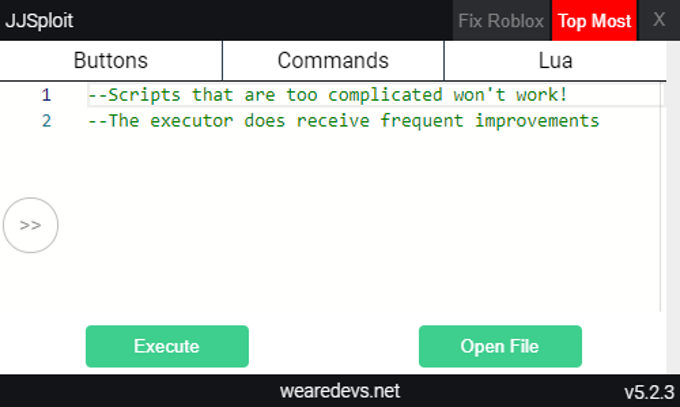 JJSploit Information WeAreDevs, 49% OFF24 outubro 2024
JJSploit Information WeAreDevs, 49% OFF24 outubro 2024 -
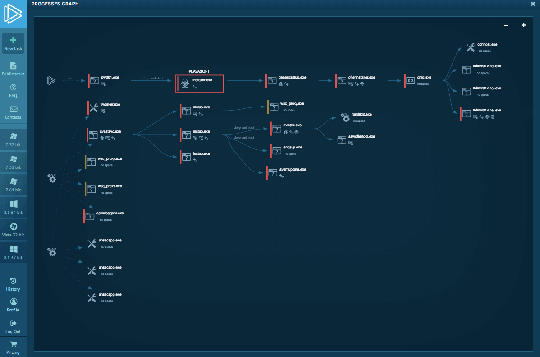
 Malware analysis Malicious activity24 outubro 2024
Malware analysis Malicious activity24 outubro 2024 -
 Random require script appearing each time I login to studio - Scripting Support - Developer Forum24 outubro 2024
Random require script appearing each time I login to studio - Scripting Support - Developer Forum24 outubro 2024 -
 Malware analysis Malicious activity24 outubro 2024
Malware analysis Malicious activity24 outubro 2024 -
 JJsPLOIT Tutorial #Exploit #tutorial #WeAreDevs #scripting24 outubro 2024
JJsPLOIT Tutorial #Exploit #tutorial #WeAreDevs #scripting24 outubro 2024 -
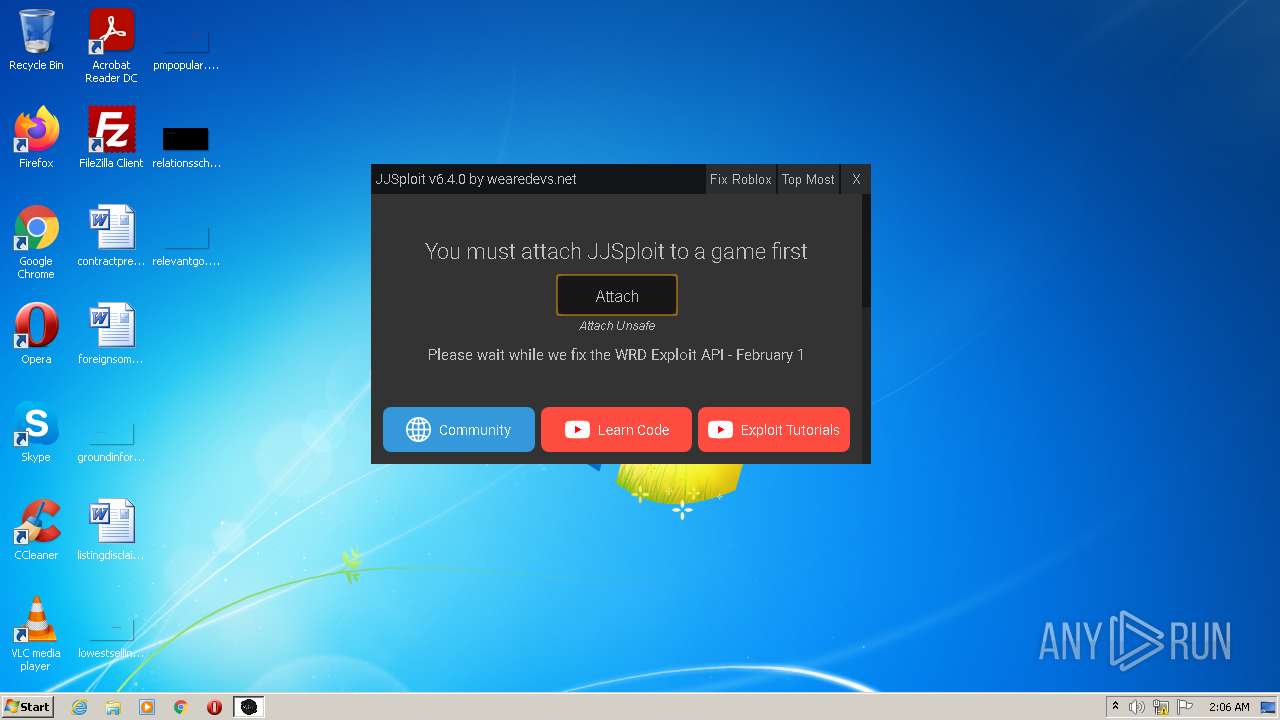 Malware analysis Malicious24 outubro 2024
Malware analysis Malicious24 outubro 2024 -
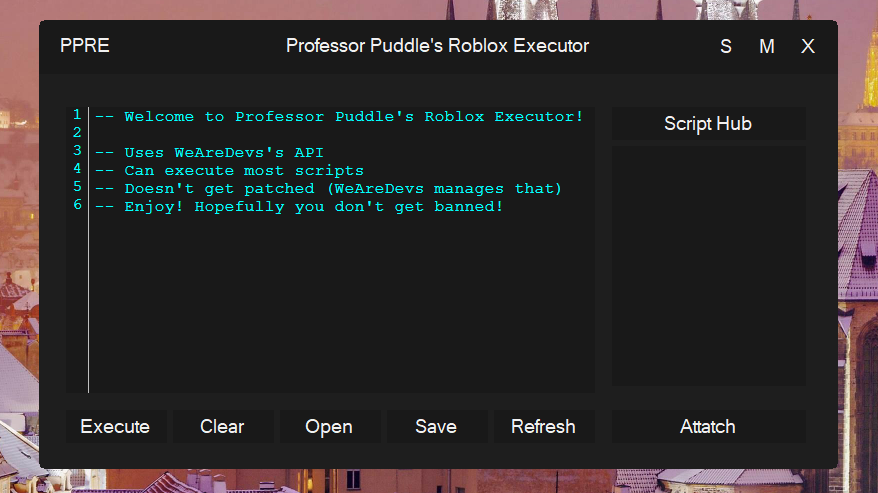 GitHub - Professor-Puddle/Roblox-Executor: An awesome Roblox Executor that uses WeAreDevs's API. Can execute most scripts, including Eclipse Hub, and has it's own bootstrapper. Read the README file of this repository for mor24 outubro 2024
GitHub - Professor-Puddle/Roblox-Executor: An awesome Roblox Executor that uses WeAreDevs's API. Can execute most scripts, including Eclipse Hub, and has it's own bootstrapper. Read the README file of this repository for mor24 outubro 2024 -
 Exploiter kicking everyone from the server, how to find who24 outubro 2024
Exploiter kicking everyone from the server, how to find who24 outubro 2024
você pode gostar
-
 Mostra de ícones de computador de cavalo pulando hipismo, cavalo, cavalo, branco, mamífero png24 outubro 2024
Mostra de ícones de computador de cavalo pulando hipismo, cavalo, cavalo, branco, mamífero png24 outubro 2024 -
 Nissan Dayz 2020 Key FOB duplicate required Karachi - Nissan24 outubro 2024
Nissan Dayz 2020 Key FOB duplicate required Karachi - Nissan24 outubro 2024 -
 My LEGO Harry Potter Minifigure Collection - 2020 Edition (100+24 outubro 2024
My LEGO Harry Potter Minifigure Collection - 2020 Edition (100+24 outubro 2024 -
 O que significa e como usar WONDER?24 outubro 2024
O que significa e como usar WONDER?24 outubro 2024 -
 Casais de mestre-sala e porta-bandeira: parceria que encanta24 outubro 2024
Casais de mestre-sala e porta-bandeira: parceria que encanta24 outubro 2024 -
 Episode 1, Sono Bisque Doll wa Koi wo suru Wiki24 outubro 2024
Episode 1, Sono Bisque Doll wa Koi wo suru Wiki24 outubro 2024 -
 R.S.C. Anderlecht - Wikipedia24 outubro 2024
R.S.C. Anderlecht - Wikipedia24 outubro 2024 -
What saga should I watch after the Kid Buu Saga in DBZ? - Quora24 outubro 2024
-
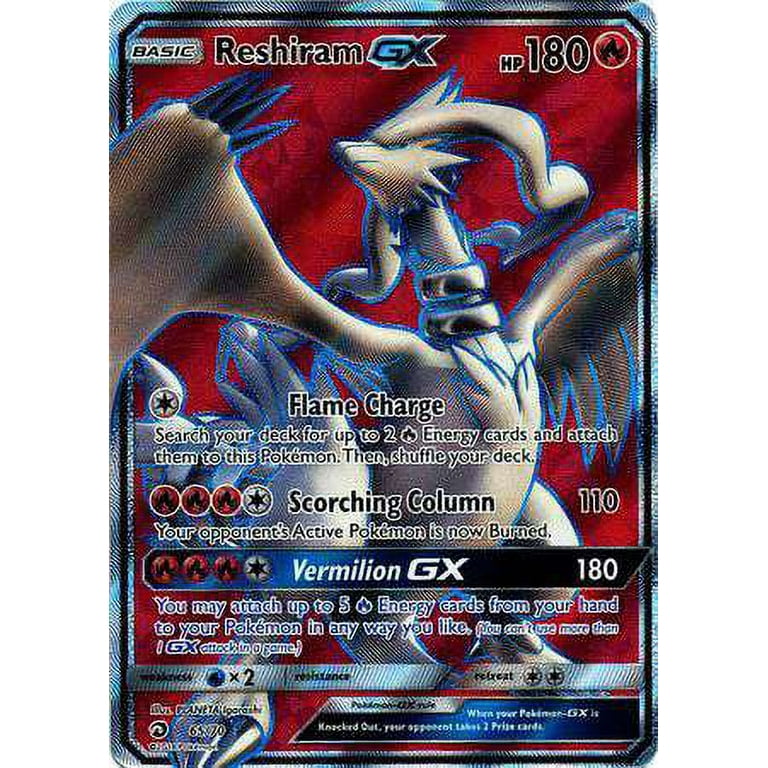 Pokemon Dragon Majesty Reshiram-GX #6524 outubro 2024
Pokemon Dragon Majesty Reshiram-GX #6524 outubro 2024 -
 JAN238017 - SCP FOUNDATION SERIES MTF ZETA-9 MOLE RATS 1/12 AF - Previews World24 outubro 2024
JAN238017 - SCP FOUNDATION SERIES MTF ZETA-9 MOLE RATS 1/12 AF - Previews World24 outubro 2024