Indirect Command Execution – Penetration Testing Lab
Por um escritor misterioso
Last updated 27 outubro 2024

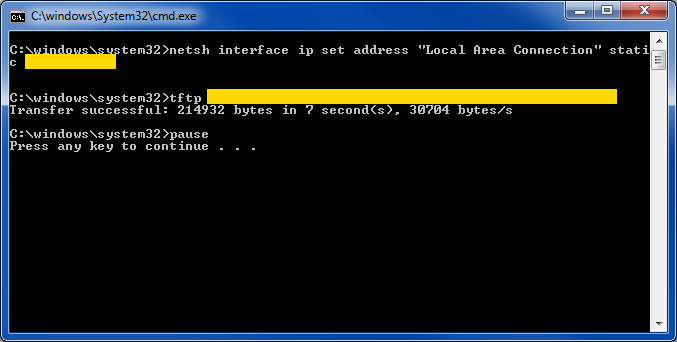
The windows ecosystem provides multiple binaries that could be used by adversaries to execute arbitrary commands that will evade detection especially in environments that are monitoring binaries such as "cmd.exe". In certain occasions the techniques described below could be used to bypass application whitelisting products if rules are not configured properly (whitelist by path or…

Indirect Command Execution: Defense Evasion (T1202) - Hacking Articles
Next level for Siemens Industrial Edge: New cloud service, more devices, and low-code integration, Press, Company
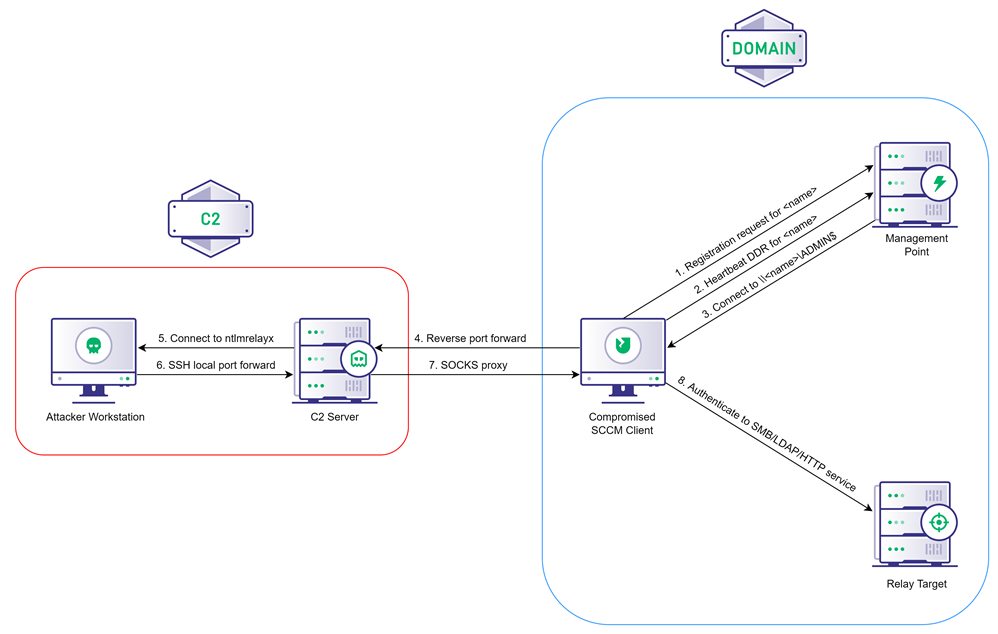
Coercing NTLM Authentication from SCCM, by Chris Thompson

Denial-of-service attack - Wikipedia
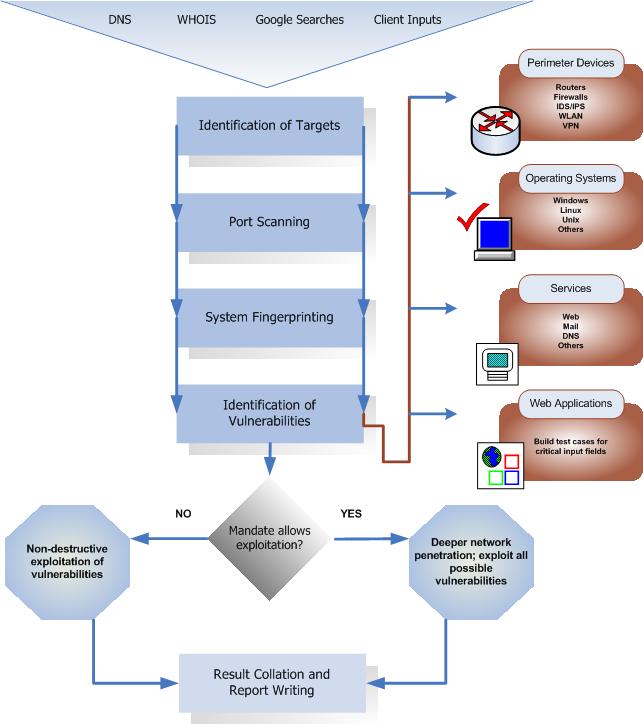
Penetration Testing Execution Standard
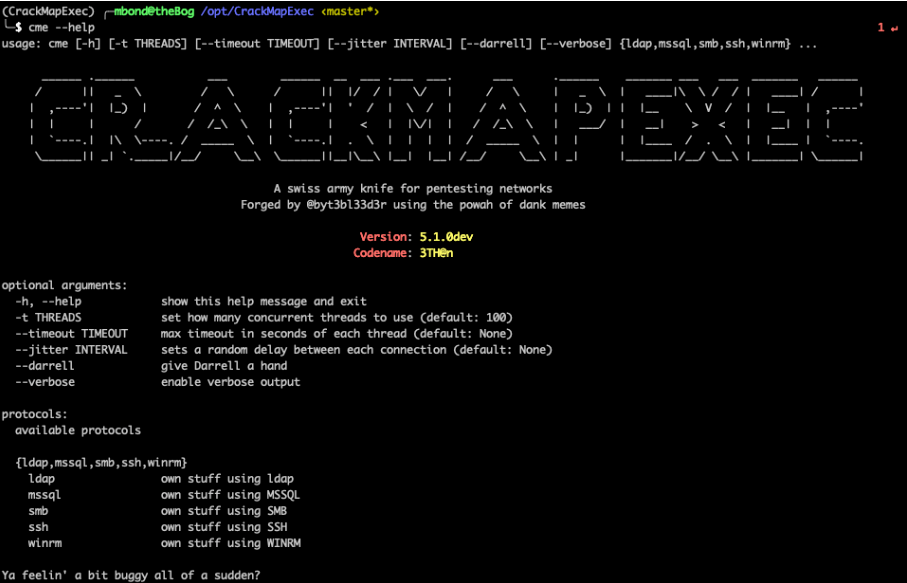
CrackMapExec Basics. One of the tools that I like to use…, by Mike Bond

command execution walkthrough – Penetration Testing Lab

Indirect Command Execution: Defense Evasion (T1202) - Hacking Articles
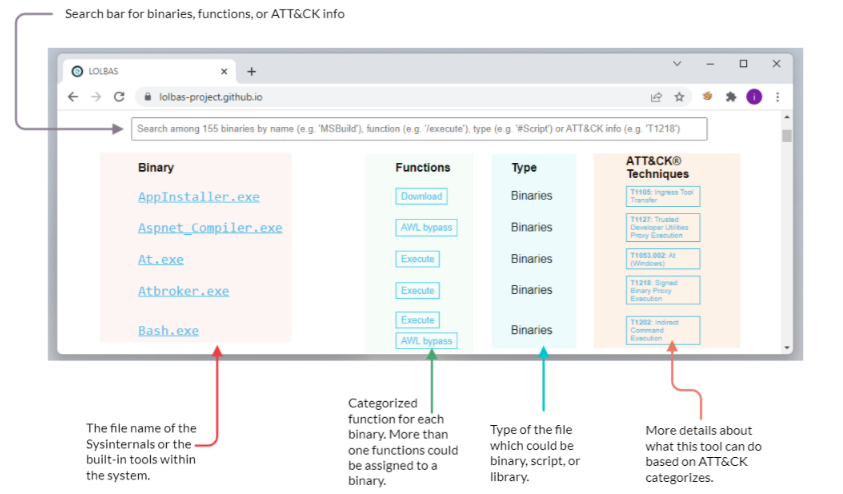
TRY HACK ME: Living Off The Land Write-Up, by Shefali Kumari
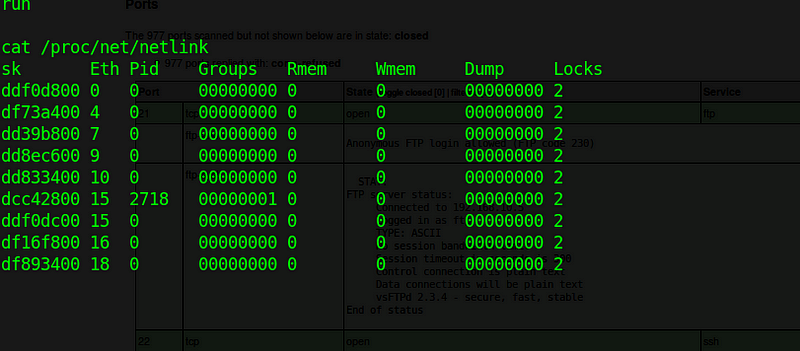
Basic Penetration testing lab — 1 – Sahil Ahamad - Information Security Blog – Product Security at Facebook
Recomendado para você
-
 Understanding Command Line Arguments and How to Use Them27 outubro 2024
Understanding Command Line Arguments and How to Use Them27 outubro 2024 -
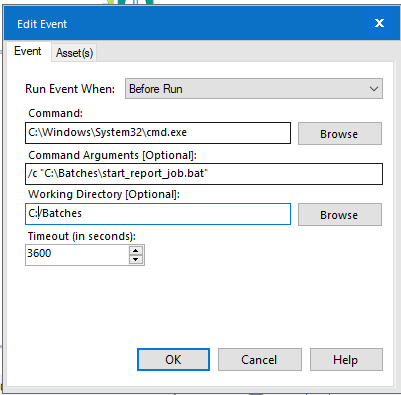
Solved: How to Run System Exec (Batch File) as an Admin - NI Community27 outubro 2024
-
 CustomCmd/Run bat/Read File/Run Exe in Code Plugins - UE Marketplace27 outubro 2024
CustomCmd/Run bat/Read File/Run Exe in Code Plugins - UE Marketplace27 outubro 2024 -
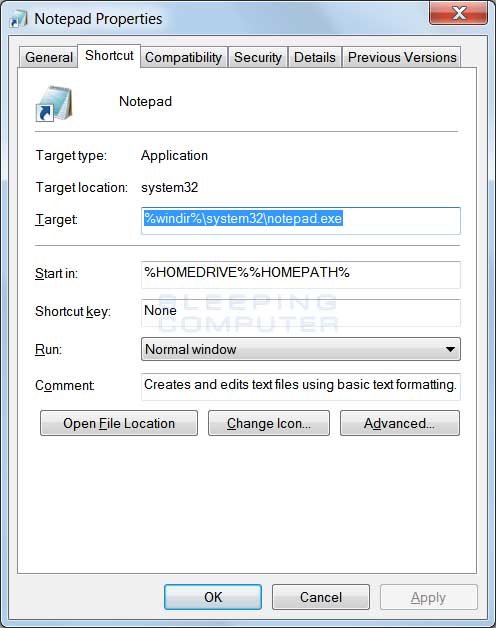
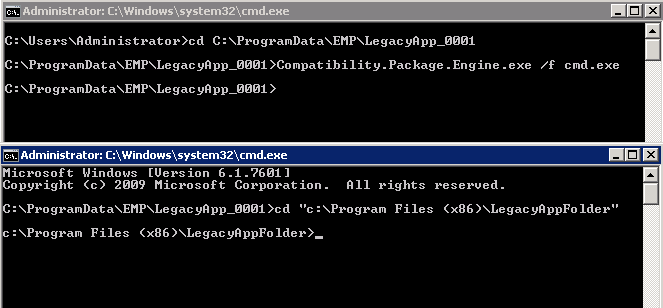 Run cmd.exe as a child process to the EMP compatibility package engine - AWS End-of-Support Migration Program (EMP) for Windows Server27 outubro 2024
Run cmd.exe as a child process to the EMP compatibility package engine - AWS End-of-Support Migration Program (EMP) for Windows Server27 outubro 2024 -
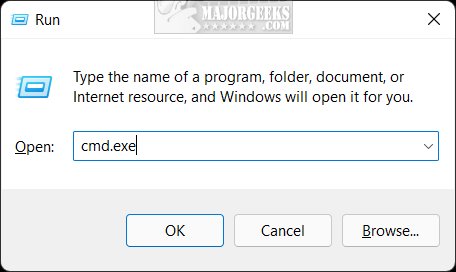 10 Ways to Open the Command Prompt in Windows 11 - MajorGeeks27 outubro 2024
10 Ways to Open the Command Prompt in Windows 11 - MajorGeeks27 outubro 2024 -
Run exe or shell command without cmd window popup · Issue #249 · espanso/espanso · GitHub27 outubro 2024
-
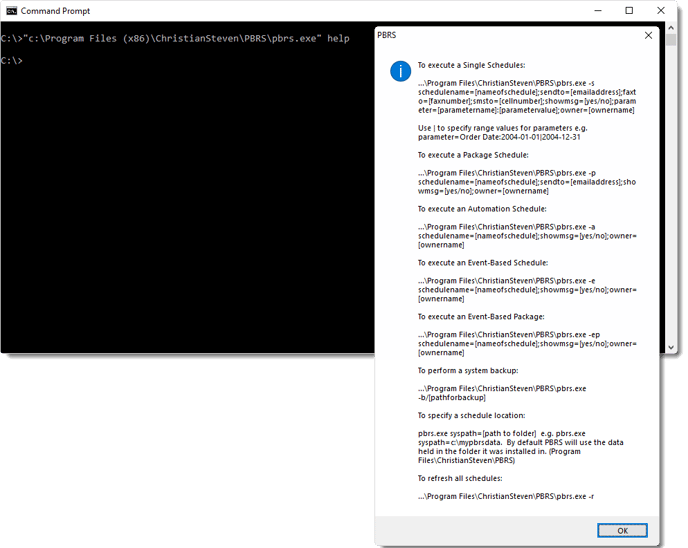 How do I use Command Line Options in PBRS?27 outubro 2024
How do I use Command Line Options in PBRS?27 outubro 2024 -
 windows - Task Sheduler: How to run batch file through cmd instead of taskeng.exe? - Stack Overflow27 outubro 2024
windows - Task Sheduler: How to run batch file through cmd instead of taskeng.exe? - Stack Overflow27 outubro 2024 -
Solved: Cannot execute After Run command on server - Alteryx Community27 outubro 2024
-
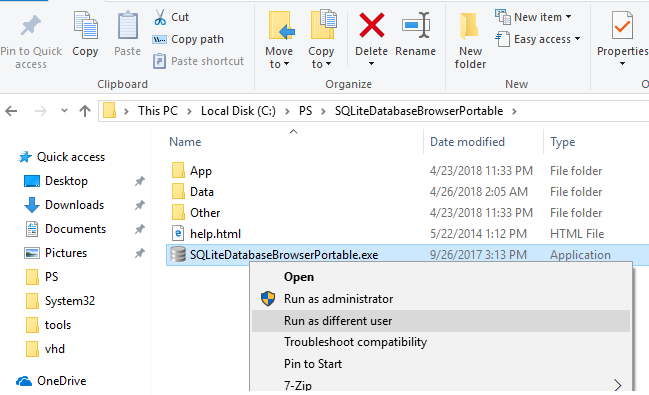 How to Run a Program as a Different User (RunAs) in Windows27 outubro 2024
How to Run a Program as a Different User (RunAs) in Windows27 outubro 2024
você pode gostar
-
/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2022/9/f/dgLmbISB2Y5BpqRqKWaQ/0iphone1.jpg) 5 truques rápidos para traduzir textos em celulares Android e iPhone27 outubro 2024
5 truques rápidos para traduzir textos em celulares Android e iPhone27 outubro 2024 -
 New Call Of Duty COD MW2 Ghost Skull Mask Biker Balaclava Face Head Wa27 outubro 2024
New Call Of Duty COD MW2 Ghost Skull Mask Biker Balaclava Face Head Wa27 outubro 2024 -
 Jogo Hora do Rush Com Desenho Mágico Para Crianças - Big Star27 outubro 2024
Jogo Hora do Rush Com Desenho Mágico Para Crianças - Big Star27 outubro 2024 -
 Liverpool é o dono do mundo pela primeira vez - Jaeci Carvalho27 outubro 2024
Liverpool é o dono do mundo pela primeira vez - Jaeci Carvalho27 outubro 2024 -
 Best Chess Olympiad Posts - Reddit27 outubro 2024
Best Chess Olympiad Posts - Reddit27 outubro 2024 -
 Ben 10 Alien Force Toy Chromastone 4 Tall Action Figure Collectible Card New27 outubro 2024
Ben 10 Alien Force Toy Chromastone 4 Tall Action Figure Collectible Card New27 outubro 2024 -
 Penalty Shooters 2 (Football) Game for Android - Download27 outubro 2024
Penalty Shooters 2 (Football) Game for Android - Download27 outubro 2024 -
 Rede de Supermercados Super Golff - Av. Saul Elkind, 186027 outubro 2024
Rede de Supermercados Super Golff - Av. Saul Elkind, 186027 outubro 2024 -
 Vs. Telefone Celular. Comparar Dois Smartphones Ilustração do Vetor - Ilustração de duelo, celular: 23511741227 outubro 2024
Vs. Telefone Celular. Comparar Dois Smartphones Ilustração do Vetor - Ilustração de duelo, celular: 23511741227 outubro 2024 -
 ranni the witch and melina (elden ring) drawn by mian_li27 outubro 2024
ranni the witch and melina (elden ring) drawn by mian_li27 outubro 2024