Algorithms, Free Full-Text
Por um escritor misterioso
Last updated 24 outubro 2024
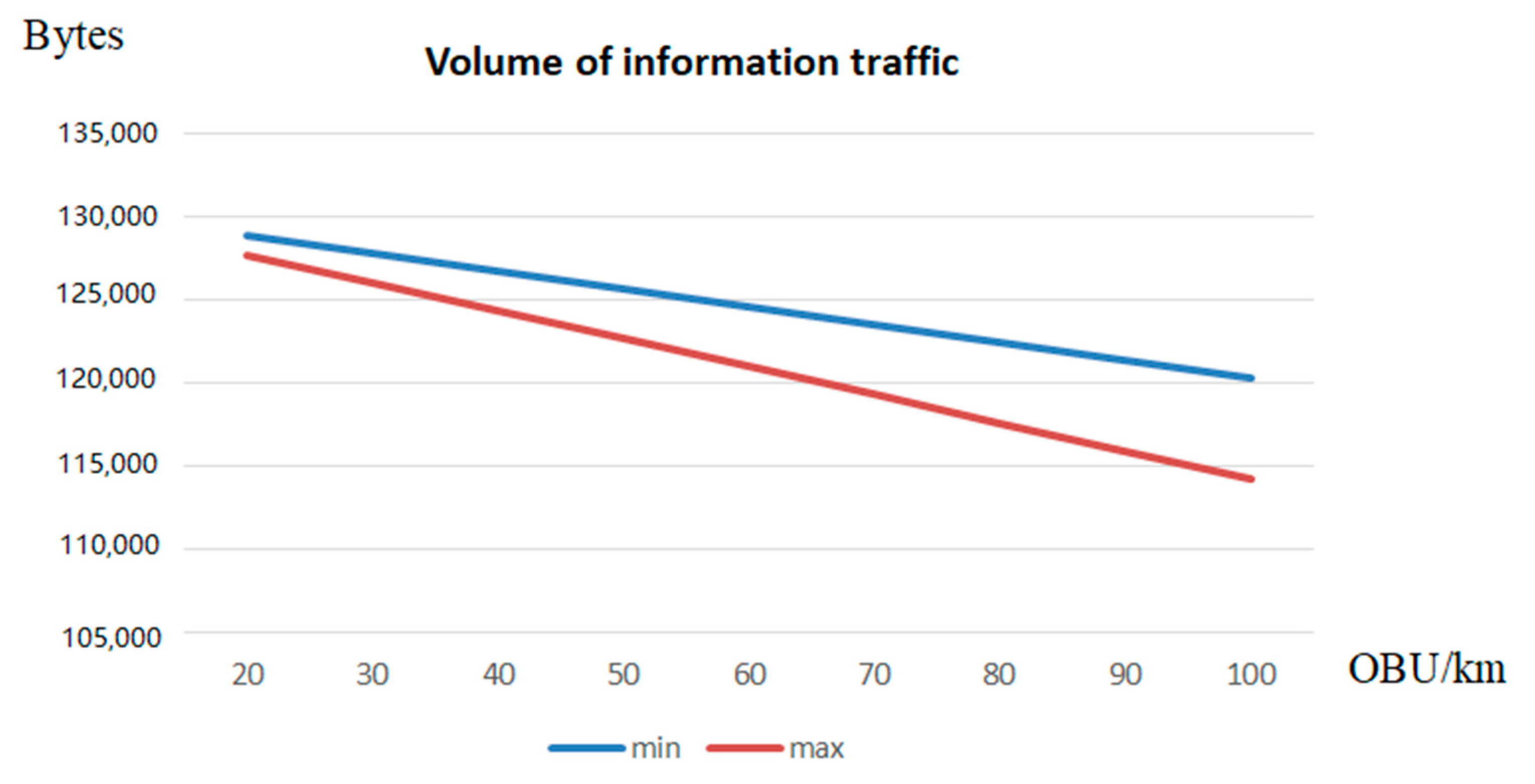
Authentication protocols are expanding their application scope in wireless information systems, among which are low-orbit satellite communication systems (LOSCS) for the OneWeb space Internet, automatic object identification systems using RFID, the Internet of Things, intelligent transportation systems (ITS), Vehicular Ad Hoc Network (VANET). This is due to the fact that authentication protocols effectively resist a number of attacks on wireless data transmission channels in these systems. The main disadvantage of most authentication protocols is the use of symmetric and asymmetric encryption systems to ensure high cryptographic strength. As a result, there is a problem in delivering keys to the sides of the prover and the verifier. At the same time, compromising of keys will lead to a decrease in the level of protection of the transmitted data. Zero-knowledge authentication protocols (ZKAP) are able to eliminate this disadvantage. However, most of these protocols use multiple rounds to authenticate the prover. Therefore, ZKAP, which has minimal time costs, is developed in the article. A scheme for adapting protocol parameters has been developed in this protocol to increase its efficiency. Reductions in the level of confidentiality allow us to reduce the time spent on the execution of the authentication protocol. This increases the volume of information traffic. At the same time, an increase in the confidentiality of the protocol entails an increase in the time needed for authentication of the prover, which reduces the volume of information traffic. The FPGA Artix-7 xc7a12ticsg325-1L was used to estimate the time spent implementing the adaptive ZKAP protocol. Testing was performed for 32- and 64-bit adaptive authentication protocols.
Algorithms of Education — University of Minnesota Press

ACLS algorithm overview
An Overview of QuickSort Algorithm, by Harshil Patel

Machine Learning Algorithms - Second Edition

What is A* Search Algorithm? A* (star) Algorithm in AI 2024
Data Structures and Algorithms Online Courses : Free and Paid

How the Instagram Algorithm Works (Updated 2023)
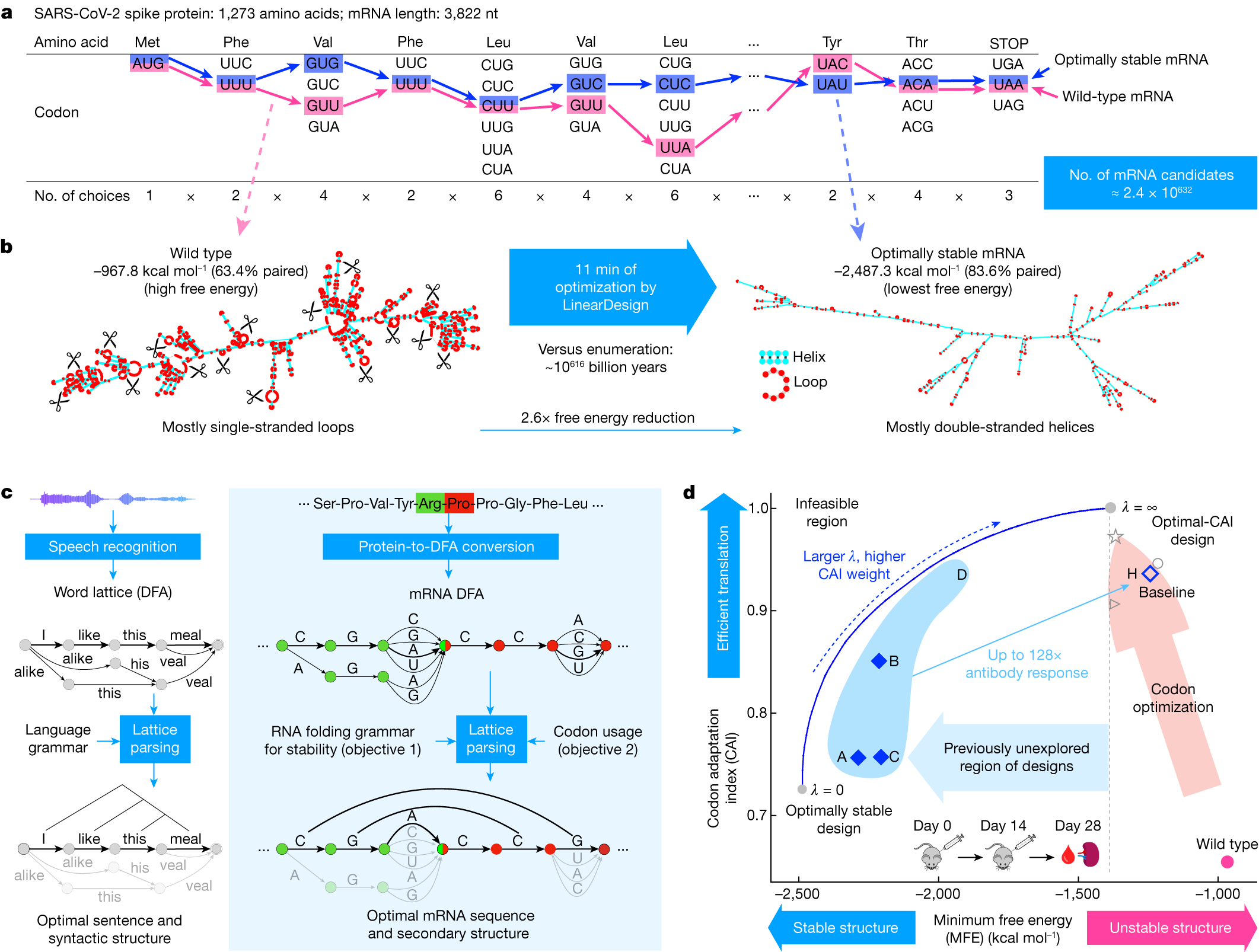
Algorithm for optimized mRNA design improves stability and
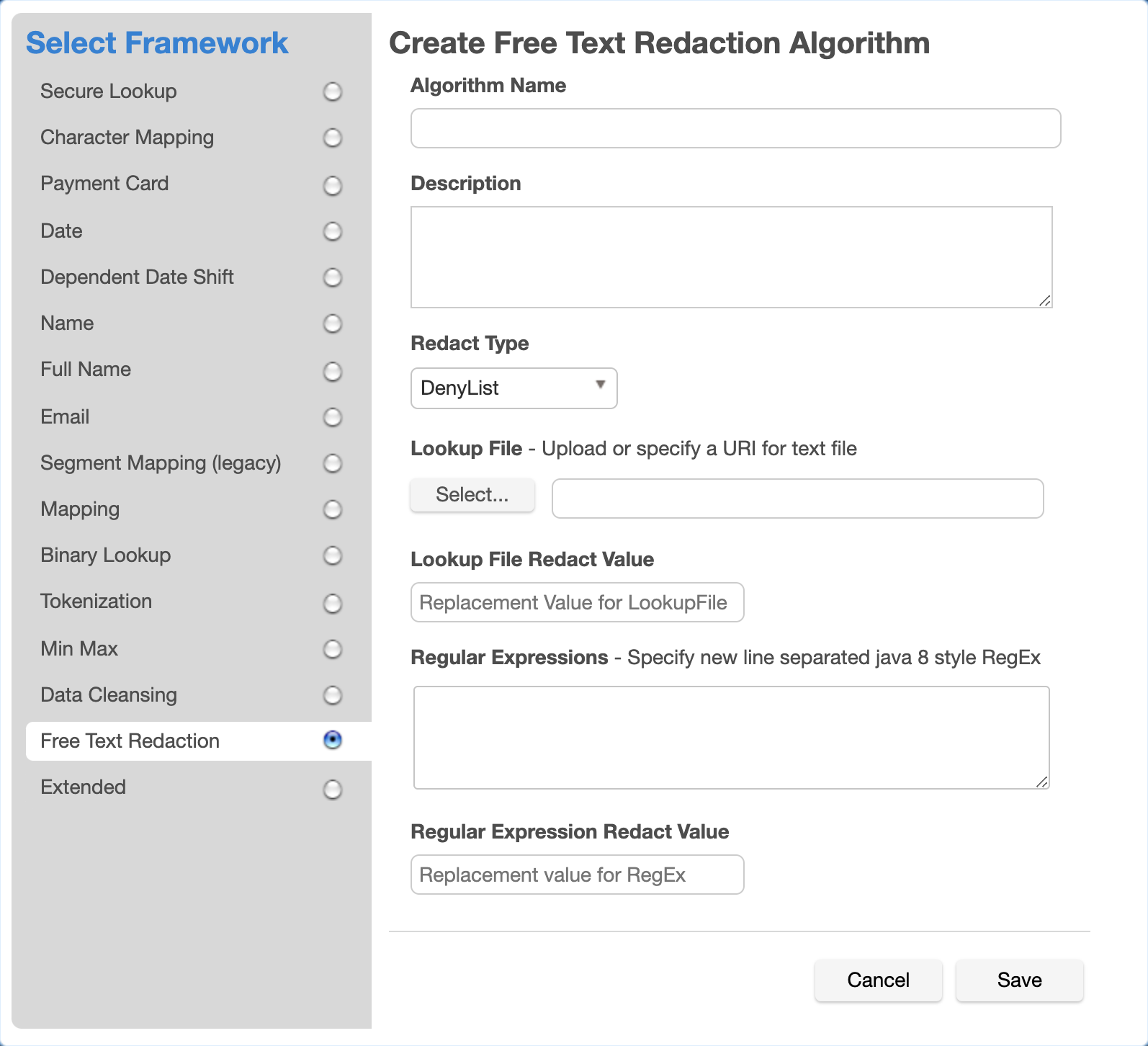
Free Text Redaction - Delphix Masking 6.0.17
RePub, Erasmus University Repository: Algorithms as Folding
Algorithms : Free Download, Borrow, and Streaming : Internet Archive
Recomendado para você
-
 Anime Lost Simulator Codes - Roblox24 outubro 2024
Anime Lost Simulator Codes - Roblox24 outubro 2024 -
![135K CODE] Project New World, Roblox GAME, ALL SECRET CODES, ALL WORKING CODES](https://i.ytimg.com/vi/uA5Ij2VwemU/sddefault.jpg) 135K CODE] Project New World, Roblox GAME, ALL SECRET CODES, ALL WORKING CODES24 outubro 2024
135K CODE] Project New World, Roblox GAME, ALL SECRET CODES, ALL WORKING CODES24 outubro 2024 -
 What Dev fruit code?! New Sea beast.. ROBLOX Project New World Codes !24 outubro 2024
What Dev fruit code?! New Sea beast.. ROBLOX Project New World Codes !24 outubro 2024 -
 10 Best Free C Programming Courses to Take in 2023 — Class Central24 outubro 2024
10 Best Free C Programming Courses to Take in 2023 — Class Central24 outubro 2024 -
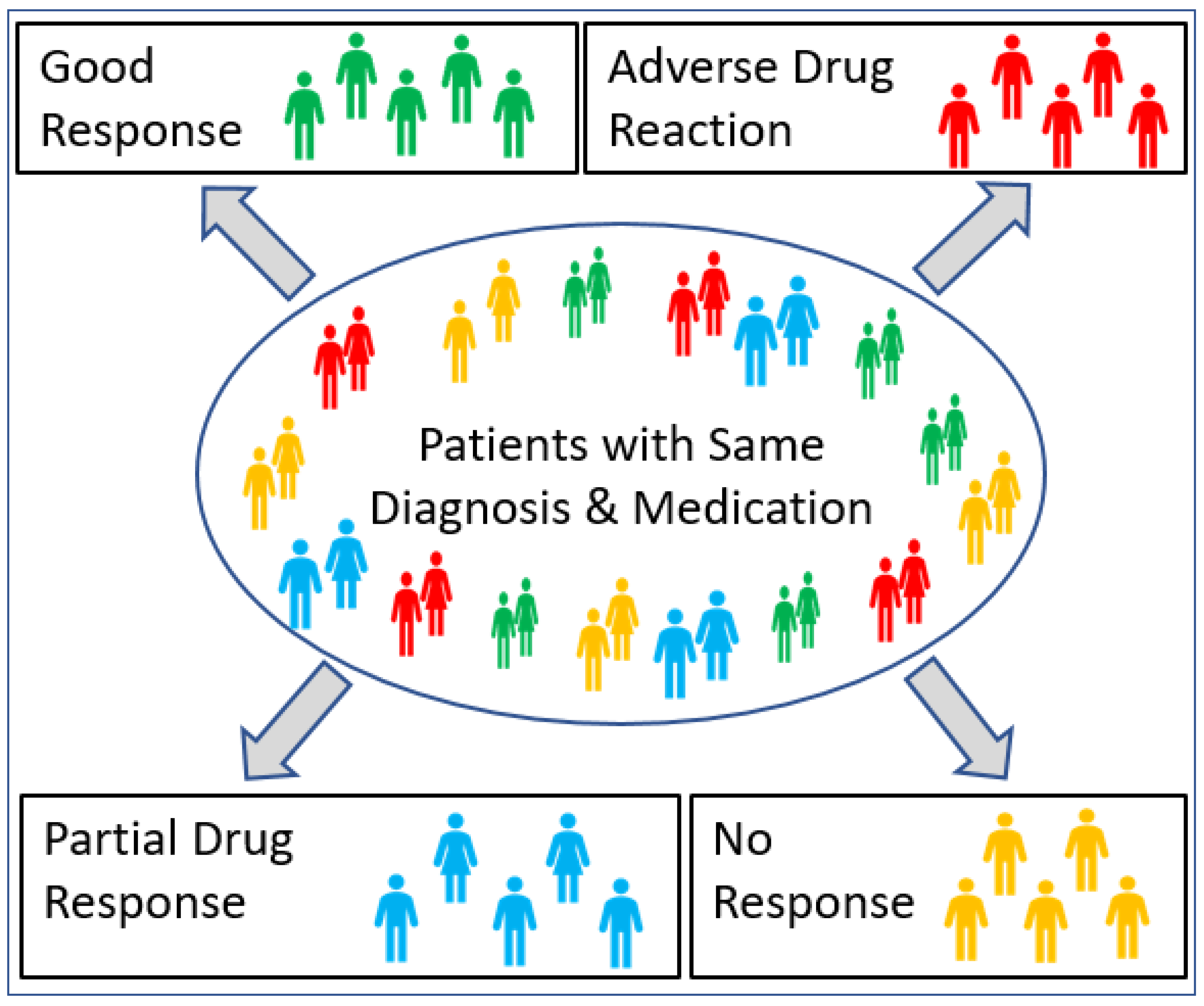 JPM, Free Full-Text24 outubro 2024
JPM, Free Full-Text24 outubro 2024 -
The Role of sound groundwater resources management and governance to achieve water security24 outubro 2024
-
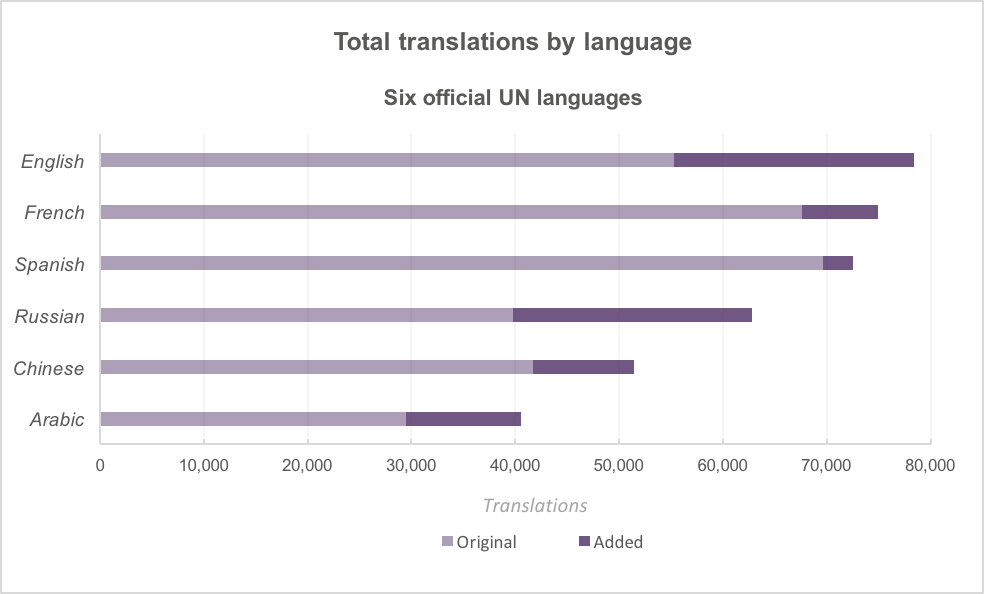 Increasing Name Translations in Who's On First, by Postzen, postzen24 outubro 2024
Increasing Name Translations in Who's On First, by Postzen, postzen24 outubro 2024 -
Combined Experimental and Mechanoelastic Modeling Studies on the Low-Spin Stabilized Mixed Crystals of 3D Oxalate-Based Coordination Materials24 outubro 2024
-
 *NEW* ALL WORKING CODES FOR PROJECT NEW WORLD IN 2022! ROBLOX PROJECT NEW WORLD CODES24 outubro 2024
*NEW* ALL WORKING CODES FOR PROJECT NEW WORLD IN 2022! ROBLOX PROJECT NEW WORLD CODES24 outubro 2024 -
 ALL NEW *SECRET* XMAS UPDATE CODES in PROJECT NEW WORLD CODES! (Roblox Project New World Codes)24 outubro 2024
ALL NEW *SECRET* XMAS UPDATE CODES in PROJECT NEW WORLD CODES! (Roblox Project New World Codes)24 outubro 2024
você pode gostar
-
 Iori Yagami (Character) - Comic Vine24 outubro 2024
Iori Yagami (Character) - Comic Vine24 outubro 2024 -
withdrawal record - Funny Games Online Casino24 outubro 2024
-
 Sua vida gatinho de gente!24 outubro 2024
Sua vida gatinho de gente!24 outubro 2024 -
 /images/anime/10/67587.jpg24 outubro 2024
/images/anime/10/67587.jpg24 outubro 2024 -
 Desenho de cachorro grande para colorir24 outubro 2024
Desenho de cachorro grande para colorir24 outubro 2024 -
 Italian Calcio League Serie A24 outubro 2024
Italian Calcio League Serie A24 outubro 2024 -
 xadrez. conjunto de peças de xadrez preto. cavalo, torre, peão, bispo, rei, rainha. imagem vetorial. 9173309 Vetor no Vecteezy24 outubro 2024
xadrez. conjunto de peças de xadrez preto. cavalo, torre, peão, bispo, rei, rainha. imagem vetorial. 9173309 Vetor no Vecteezy24 outubro 2024 -
 Fantasia Vampira Infantil de Halloween Vestido Super Luxo e dentes24 outubro 2024
Fantasia Vampira Infantil de Halloween Vestido Super Luxo e dentes24 outubro 2024 -
90nd Stoppage (@90ndstoppage) • Instagram photos and videos24 outubro 2024
-
 Poor Chuuya (the real one) : r/BungouStrayDogs24 outubro 2024
Poor Chuuya (the real one) : r/BungouStrayDogs24 outubro 2024